The techniques for wallet security are an array of both technological and procedural steps taken to ensure that digital wallets are protected from any threats including hacking and fraud. Such techniques may include encryption using AES-256, MFA, private key protection, constant security assessment, securing the APIs and educating end-users. These practices enable users to safely store and exchange their digital assets within mobile wallets, crypto wallets, and fintech solutions.
Introduction
With an ever-growing trend toward digital payments, cryptocurrency networks, and fintech applications, there emerges a need to have secure wallets. The reason for this is that digital wallets hold highly valuable assets, including private keys, payment information, and transaction records.
For this reason, it becomes necessary to apply best practices related to wallet security to prevent any irreparable financial damage.
Why Wallet Security is Important?
Wallets have been used extensively in various applications such as cryptocurrency exchanges, UPI-based payment gateways, and banking applications. Due to the involvement of money, wallets are one of the favorite targets for phishing attacks, malware attacks, API attacks, and credential theft.
Practically, most attacks on wallets happen not because of some sophisticated hacking process but because of weak authentication systems, unsafe private key storage, and vulnerable backend API.
Using AES-256 and TLS 1.3 for encryption
Storing private keys securely with HSM/MPC
Enforcing MFA for all kinds of login
Penetration testing and security auditing
Securing API development with OAuth 2.0
Real-time fraud detection and monitoring
Phishing protection
OWASP guidelines compliant secure coding
Compliance with regulations such as GDPR, KYC, AML
Backup/recovery system encryption
1. Strong Encryption Protocols
Encryption lies at the core of wallet security. This means that even if any data gets compromised, it will remain safe due to proper encryption protocols.
Using AES-256 protocol for encryption of stored data
Using TLS 1.3 for communication channel encryption
Not storing private keys in plaintext
2. Secure Management of Private Keys
Private keys are the most sensitive element within any wallet ecosystem.
Best practices to implement:
Use of HSMs for key management
Use of MPC to split key management among parties
Use of secure seed phrases
Avoid centralization of private keys
3. Multi-Factor Authentication (MFA)
MFA offers a vital step up from using passwords alone.
Popular MFA techniques include:
One-time password generation
Biometric identification (touch ID)
Application-based MFA
4. Security of APIs and Backends
Many applications have extensive use of APIs for executing transactions and accessing accounts.
API security features should be:
OAuth 2.0 authentication
API rate limiting
Validation of inputs
Monitoring of APIs
A secure backend system plays a critical role for platforms such as online banking and crypto exchanges.
5. Fraud Detection through Real-Time Monitoring
Real-time monitoring should be implemented by modern wallet systems.
Examples include:
Use of AI for fraud detection
Analyzing user behavior for anomalies
Sending notifications for suspicious activities
Risk scoring and other metrics
This practice is widely applied in financial technology solutions.
6. Safe Software Development Practices
Safe coding practices form one of the key pillars of wallet security.
Develop applications using:
OWASP standards for application security
No hardcoding of authentication credentials
Reputable libraries and frameworks
Dependency updates
7. Continuous Security Audits
Regular testing ensures robustness in the face of any attacks.
Penetration testing (ethical hacking)
Security audits by third parties
Vulnerability assessment software
Logging and continuous monitoring
The wallet solutions have to meet global regulatory requirements to establish trust and maintain legal standing.
GDPR for data privacy
KYC (Know Your Customer) checks
AML (Anti-Money Laundering) measures
Audit trail security
9. Backups and Recovery Processes
Users cannot lose their assets when they fail to gain access to their wallets.
Encrypted cloud backup services
Seed phrase recovery mechanism
Multidevice sync capabilities
Key regeneration procedures
Expert Insight
In practical wallet development projects, the commonest security vulnerabilities do not emanate from sophisticated cryptographic weaknesses but rather from technical implementation errors like insecure APIs, weak authentication protocols, and ineffective key management systems.
Conclusion
The security of a wallet is not a task that should be done once but rather an ongoing activity that involves having high-end encryption, secure architecture, regulations compliances, and more awareness among the users. The increase in the number of digital financial services calls for increased concern for the security of these applications.
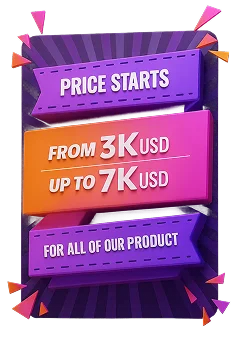
If you are thinking about developing a secure wallet ,As a Crypto Wallet Development Company we can help you to provide solutions for secure and scalable wallets.
Customer feedback and reviews are our major concerns! Here we have shared a Ratings of our reputed clients







You let us know what you need, Technical experts will call to review your needs in detail.We promise to keep all information private.